What Is Hacking? Types of Hackers Explained – Best Cybersecurity Guide for Beginners in 2026
Learn what hacking is and understand the Types of Hackers including white hat, black hat, and Gray hat. A complete cybersecurity guide with techniques, examples, and FAQs.
Introduction
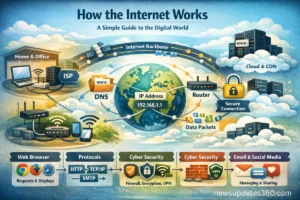
The internet has become a vital part of everyday life. From online banking and shopping to communication and entertainment, almost every activity now depends on digital technology. However, with the rapid growth of the internet, cyber threats have also increased significantly. One of the most commonly discussed topics in cybersecurity is hacking.
Hacking refers to the process of identifying vulnerabilities in computer systems, networks, or software and exploiting them to gain access or control. While many people associate hacking with illegal activities, not all hackers have malicious intentions. In fact, some professionals use hacking techniques to improve security and protect systems.
To understand the cybersecurity world better, it is important to learn about the Types of Hackers and their different motivations. Some hackers work to protect systems, while others attempt to exploit vulnerabilities for financial gain or political purposes. Knowing the various Types of Hackers helps individuals and organizations understand how cyber attacks happen and how they can prevent them.
This article provides a detailed explanation of hacking, how it works, the motivations behind it, and the different categories of hackers operating in the digital world today.
What Is Hacking?
Hacking is the act of gaining unauthorized access to computer systems or networks by exploiting security weaknesses. Hackers often use advanced technical skills and specialized tools to bypass security controls and access restricted data or systems.
Originally, the term “hacker” was used to describe skilled programmers who enjoyed exploring technology and solving complex problems. Over time, the meaning changed and became associated with cybercriminal activities.
Today, hacking can be both legal and illegal, depending on the intent. Ethical hackers work with organizations to strengthen cybersecurity, while malicious hackers attempt to exploit systems for personal benefit.
Understanding hacking also involves understanding the various Types of Hackers who operate in cyberspace. Each group has different goals, skills, and approaches when interacting with digital systems.

How Hacking Works
Most cyber attacks follow a structured process. Hackers usually go through several stages before gaining access to a system.
1. Information Gathering
The first stage involves collecting information about the target system. Hackers may gather details such as IP addresses, domain names, system architecture, and employee information. This phase helps them understand how the system works.
2. Scanning
Once information is collected, hackers scan the system for vulnerabilities. Tools are used to detect open ports, weak security configurations, or outdated software that can be exploited.
3. Exploitation
In this stage, hackers use vulnerabilities to gain unauthorized access. They may use malware, password cracking tools, or social engineering attacks.
4. Maintaining Access
Hackers often install backdoors or hidden programs that allow them to return to the system later without repeating the attack.
5. Covering Tracks
Finally, hackers remove evidence of their activities to avoid detection by security teams.
Top 10 Global Innovations future technologies 2030 that Will Change the World
Different Types of Hackers in Cybersecurity
Understanding the Types of Hackers is essential for learning how cyber attacks occur and how organizations defend against them. Hackers are usually classified based on their intentions and activities.

1. White Hat Hackers
White hat hackers are ethical cybersecurity professionals who use their technical skills to protect computer systems. Organizations hire them to identify vulnerabilities before criminals can exploit them.
These professionals perform penetration testing, security audits, and vulnerability assessments to improve digital security. Their work helps organizations protect sensitive information and prevent cyber attacks.
White hat hackers follow strict legal guidelines and always operate with permission from system owners.
2. Black Hat Hackers
Black hat hackers are individuals who break into systems for malicious purposes. They may steal personal data, financial information, or confidential business records.
These hackers often create malware, conduct phishing attacks, or exploit security flaws to gain access to systems. Their activities are illegal and can cause significant financial and reputational damage to organizations.
Black hat hackers are among the most dangerous Types of Hackers because they intentionally harm individuals, companies, and governments.
3. Gray Hat Hackers
Gray hat hackers operate between ethical and malicious hacking. They may access systems without permission but typically do not intend to cause harm.
In some cases, they discover vulnerabilities and inform the organization about them. However, since they accessed the system without authorization, their actions may still violate legal regulations.
This group represents one of the more controversial Types of Hackers because their intentions may be positive but their methods are not always legal.
4. Script Kiddies
Script kiddies are inexperienced hackers who rely on existing hacking tools developed by others. They usually lack deep technical knowledge but use automated programs to launch attacks.
Their actions often include website defacement, minor cyber attacks, or online pranks. Although they are not highly skilled, script kiddies can still cause disruptions to systems and services.
Many beginners exploring hacking tools fall into this category among the different Types of Hackers.

5. Hacktivists
Hacktivists use hacking as a form of political or social activism. Their goal is to promote ideological causes rather than financial gain.
They may target government agencies, corporations, or organizations that they believe are unethical. Hacktivists often conduct website defacements, data leaks, or denial-of-service attacks to spread their message.
Among the various Types of Hackers, hacktivists focus primarily on activism and public awareness.
6. State-Sponsored Hackers
State-sponsored hackers are employed or supported by governments to conduct cyber espionage and digital warfare.
These hackers target foreign governments, military systems, and critical infrastructure to gather intelligence or disrupt operations.
Because they often have significant resources and advanced training, they are considered one of the most sophisticated Types of Hackers in the cybersecurity landscape.
Common Hacking Techniques
Hackers use several techniques to exploit vulnerabilities in digital systems.
Phishing
Phishing attacks trick users into revealing sensitive information through fake emails or websites that appear legitimate.
Malware
Malware is malicious software designed to damage systems or steal data. Examples include viruses, ransomware, spyware, and trojans.
SQL Injection
SQL injection attacks exploit database vulnerabilities by inserting malicious queries into website input fields.
Password Cracking
Hackers attempt to guess or break passwords using brute force attacks or dictionary attacks.
Denial-of-Service Attacks
These attacks overload servers with excessive traffic, preventing legitimate users from accessing services.
Game-Changing Multimodal Generative AI: Redefining Intelligent Workflows in 2025
Importance of Cybersecurity
Cybersecurity protects digital systems from unauthorized access and cyber attacks. As organizations increasingly rely on digital technology, protecting data has become a major priority.
Cyber attacks can lead to financial losses, identity theft, data breaches, and service disruptions. Businesses invest heavily in cybersecurity technologies and professionals to prevent such incidents.
Understanding the various Types of Hackers helps organizations design better security strategies and defence mechanisms.
How to Protect Yourself from Hackers
Individuals can take several steps to protect themselves online.
Use Strong Passwords
Create complex passwords that include letters, numbers, and symbols.
Enable Two-Factor Authentication
Two-factor authentication adds an extra security layer to online accounts.
Avoid Suspicious Links
Never click links from unknown emails or messages.
Keep Software Updated
Security updates often fix vulnerabilities that hackers could exploit.
Install Security Software
Antivirus and firewall tools help detect threats and protect devices.

Future of Hacking and Cybersecurity
Technology continues to evolve rapidly, and so do cyber threats. New technologies such as artificial intelligence, cloud computing, and the Internet of Things have introduced additional security challenges.
As cyber attacks become more advanced, the demand for cybersecurity professionals and ethical hackers is increasing worldwide. Understanding hacking techniques and the different Types of Hackers will remain crucial for maintaining secure digital environments.
Cybersecurity has become one of the fastest-growing career fields in the modern technology industry.
Game-Changing Multimodal Generative AI: Redefining Intelligent Workflows in 2025
Frequently Asked Questions
1. What is hacking?
Hacking is the process of identifying vulnerabilities in computer systems or networks and exploiting them to gain unauthorized access.
2. Who is a hacker?
A hacker is a person with technical skills who can manipulate computer systems or networks by exploiting security weaknesses.
3. What are the main Types of Hackers?
The main categories include white hat hackers, black hat hackers, gray hat hackers, script kiddies, hacktivists, and state-sponsored hackers.
4. Is hacking always illegal?
No. Ethical hacking is legal and used by organizations to test and improve security systems.
5. What is ethical hacking?
Ethical hacking involves legally testing systems for vulnerabilities so they can be fixed before criminals exploit them.
6. What tools do hackers use?
Hackers use tools for network scanning, password cracking, vulnerability testing, and malware development.
7. What is a cyber attack?
A cyber attack is an attempt to damage or gain unauthorized access to digital systems or networks.
8. How do hackers steal passwords?
Hackers use phishing, malware, brute force attacks, and data breaches to steal passwords.
9. Can someone become an ethical hacker?
Yes. Anyone with knowledge of networking, programming, and cybersecurity can become an ethical hacker through training and certifications.
10. Why is cybersecurity important?
Cybersecurity protects digital systems from attacks, prevents data theft, and ensures the safe operation of online services.
Conclusion
Hacking is a complex topic that involves both positive and negative aspects. While malicious hackers attempt to exploit systems for personal gain, ethical hackers work to strengthen cybersecurity and protect digital infrastructure.
Learning about hacking methods and the different Types of Hackers helps individuals and organizations understand potential cyber threats. With the increasing reliance on digital technology, cybersecurity awareness is more important than ever.
By implementing strong security practices and staying informed about cyber threats, users can significantly reduce the risk of cyber attacks and protect their valuable data.
For more info visit fortinet.com
Related Updates
- Samsung Galaxy S26 Ultra Unveiled: Incredible Features, Powerful AI & Game-Changing Specs
- How the Internet Works: A Complete and Simple Explanation for Everyone in 2026
- Generative AI in 2025: Revolutionizing Everyday Life Like Never Before
- Top 10 Global Innovations future technologies 2030 that Will Change the World
- National Scholarship of India 2025 (NSP): Ultimate & Easy Process to Apply Online